Mr. Robot (MEDIUM)— THM
- Rahul Kumar

- Feb 25, 2022
- 2 min read
Updated: Mar 10, 2022
In this write-up, we are going to hack MR. Robot theme machine on try hack me

From the Nmap scan.
nmap -sV -sC -oA nmap/mrrobot <MACHINE IP>

we got three ports open 22 ssh, 80 HTTP & 443 HTTPS.
let's start with port 80 first.

well, the home page looks lit 🔥🔥 like they show in movies lol.
Checking the robots.txt file.

look like we got our first key

there is another file fsocity.dic lets see what in that

well its look like a wordlist ;>
From the directory brute-forcing , found some interesting directories
wfuzz -c -z file,/usr/share/seclists/Discovery/Web-Content/common.txt — hc 404 http://10.10.230.59/FUZZ
from the results, we can see that there are many interesting directors for us to discover
we also got a login page, we can see that it's a WordPress login dashboard

but we don't have any username or passwords (but we still have that wordlist tho)
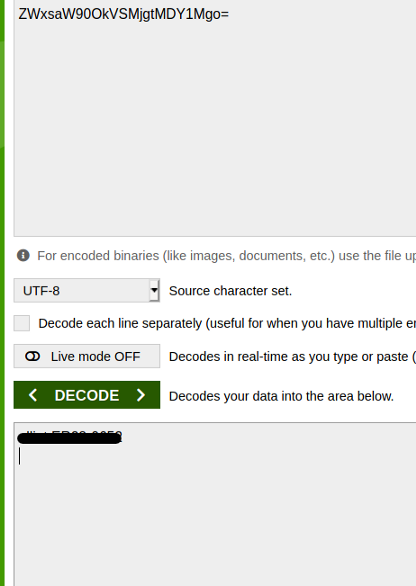
also, the /license page gives us some password with base 64 encoded

After decoding that string we got the username and password.
and can log in at the wp-admin panel

so let's get out reverse shell from the wp console.
I edit the 404-page
appearance =>editor section
and changed the code of the page. I used the pentest monkey PHP reverse shell script that can be found here https://pentestmonkey.net/tools/web-shells/php-reverse-shell .
download the tar file and extract the file

replace the 404-page code with the script code and change the IP & port to your IP address
and start an NC listener on that port.
nc -lvp <port>
update the code of the page on WordPress.

Navigate to the 404.php.

you will get the reverse connection back.

Privilege Escalation 1
- tty shell-escape

python -c ‘import pty; pty.spawn(“/bin/sh”)’background the shell using CTRL + Z, then enter
stty raw -echo; fg
export TERM=xtermIn the home directory,

we got a key but can't see/cat that and also a file with username and md5 password hash.
so let's crack it, I used the crack station for that — https://crackstation.net/

let's switch our user to “robot” with the password we cracked.
su <username>
we got our second key
Privilege Escalation 2
let's start with SUID enumeration
find / -uid 0 -perm -4000 -type f 2>/dev/nullthis command all the files with SUID set with id 0 which is the root

the Nmap one looks suspicious.
let's go to GTFO bin to see what we can do https://gtfobins.github.io
search for Nmap

On checking the version of Nmap on the host found that it's vulnerable
nmap -V
so let's exploit
nmap — interactive
!sh
let's get our last flag as root

Conclusion
This was a nice machine to exploit, especially to teach enumeration is the key. Also, the theme of the box was lit.



Comments